Welcome to The 4n6Guard Chronicles!
Hi there! Thanks for stopping by. We share in-depth cybersecurity incident analyses. Each edition will bring you real-world stories, expert insights, and actionable recommendations to help you stay ahead of the ever-evolving cyber threats. If you’re new to our community, please consider subscribing and we look forward to navigating the complex world of cybersecurity together.
Disclaimer
The company names mentioned in The 4n6Guard Chronicles are fictional, and the case studies have been modified to protect the identity of the victims. Names marked with an asterisk (*) indicate fake names used for this article. However, the impact of these cybersecurity incidents is serious and serves as a stark warning to take proactive steps to protect your company’s data. The scenarios discussed are based on real-world events and are intended to provide valuable insights and actionable recommendations to enhance your cybersecurity posture. Always consult with cybersecurity professionals to address specific needs and vulnerabilities unique to your organization.
Incident analysis case study
This case study contains three (3) sections:
-
Incident Overview: provides a comprehensive overview of the victim’s IT setup, shedding light on potential vulnerabilities and weaknesses that can be or were exploited by threat actors (“TA”).
-
Vector of Compromise or Root Causes: Provides the precise methods attackers used to infiltrate systems and the underlying issues that allowed these breaches to occur. However, in some cases, the exact mechanism may not be discovered by the limitation of the victim’s environment. In these cases, a hypothesis will be posited as the potential cause of the incident.
-
Tailored Recommendations: Expert advice on how to enhance the organization’s cybersecurity posture, with specific recommendations tailored to the type of incident covered. These recommendations may or may not be currently implemented within your company environment but should provide actionable insights.
Incident Overview
Background
ABC Company Inc. (“ABC”) operates within the manufacturing industry. Their IT infrastructure consists of an enterprise resource planning (“ERP”) system, Microsoft Office 365 (“M365”) email services, and a network of industrial control systems (“ICS”) for seamless operations. They relied on a standard Windows-based environment with Active Directory for user management, along with IoT-enabled ICS for real-time monitoring and automation. These IoT devices, managed by an internal IT department consisting of two employees, were integrated into the network to enhance operational efficiency.
Although ABC has implemented certain cybersecurity controls, the following deficiencies remain:
-
Lack of an established standard password policy which would ensure employee’s credentials were automatically reset at least every 90 days.
-
No Policy enforcing MFA enrollment for ALL users.
-
Financial transactions are frequently initiated and completed within a single email thread.
-
Email Security alerts are rarely reviewed, and the IT staff is overextended and overworked.
-
Additionally, insufficient logging further compounds these risks.
Despite being aware of these issues, management has not prioritized or allocated resources to address these critical security gaps.
Incident
On Friday, February 23, 2024, at 8:30 p.m. EST, the CEO, Steve Rogers*, received a call from one of ABC’s suppliers inquiring about a missed payment. Concerned, Steve reached out to Mary Johnson*, the Finance Department Manager, who informed him that the payment had already been made to the account specified in his email due to the supplier’s banking issues. Unbeknownst to Mary, Steve’s email account was compromised and used to send her fraudulent payment requests to process. Steve immediately raised an alert; the matter was reported to the IT department. The IT department attempted to investigate the issue but subsequently engaged a Cybersecurity Consulting firm’s aid to investigate the extent of the compromise, determine the potential exposure to sensitive data, and identify the root cause of the incident.
ABC’s IT department provided the cybersecurity consulting firm with an account that had the necessary privileges to collect forensic log data from the M365 Admin Center and Azure Portal. The M365 admin center is the web-based portal administrators use to manage user accounts and configuration settings for the M365 subscription services. It provides access to perform tasks such as, but not limited to reviewing auditing logs, adding, and removing users, changing licenses, reviewing user roles, and resetting passwords. Using the provisioned account, the consulting firm collected the necessary log data and email records and performed their review.
It is important to note that due to ABC’s license subscription to Microsoft 365 Basic Audit, only 90 days of audit record retention were available.
Vector of Compromise
During the investigation, it was discovered that the root cause of the compromise was a combination of improper password hygiene and the absence of multi-factor authentication (MFA), which led to a threat actor brute-forcing the CEO’s email account ‘Steve.rogers@abc.com’ and ultimately gaining access on Friday, January 2, 2024.
Password spraying and other types of brute-forcing are extremely common in M365 environments. It is highly recommended to enforce MFA and implement geolocation conditional access policies to reduce the chances of successful brute force attacks.
Once the threat actor gained access, they created mailbox rules designed so that any emails received from Mary’s* email account, ‘mary.johnson@abc.com’, or ABC’s Finance Department shared mailbox ‘finance@abc.com’, would be moved to the email folder called ‘Archive’ and any messages where the mailbox owner, ‘Steve.rogers@abc.com’ is in the To or CC fields; moves the message to a folder called ‘Steve Rogers‘. This would prevent Steve from seeing any of Mary’s replies to emails sent from his account by the threat actor, because they would skip his inbox and get delivered to a folder he was not aware of.
At 9:00 a.m. EST, with the CEO’s email account, the threat actor reviewed several email threads, became aware of a pending transaction and sought confirmation on the initial payment request by sending a fraudulent email to Mary’s* email account, aiming to exploit gaps in the ABC’s finance department payment verification process by demanding that it be placed on hold as soon as possible.
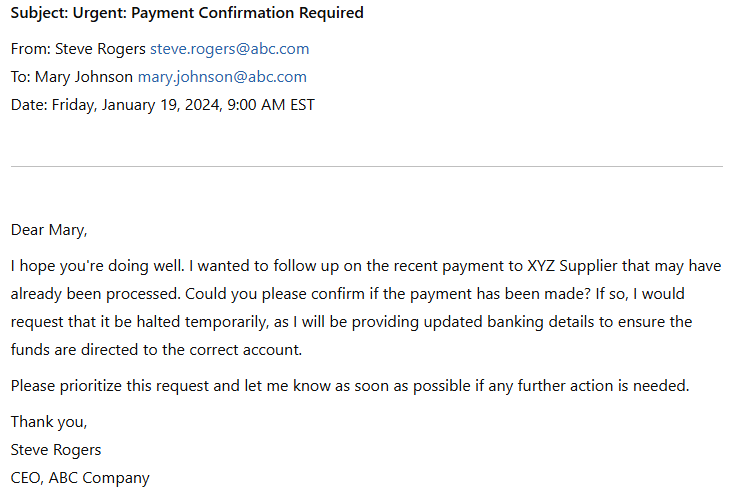
To determine if this email is authentic, the header information had to be examined as the normal body bore characteristics that match a normal email, for example, The ‘From’ and ‘To’ fields are properly populated with a legitimate sender’s email address and a legitimate recipient’s email address respectively. The ‘date and time sent’ and the ‘Subject’ fields are also properly populated. However, upon reviewing the email header, it was discovered that the source IP address originated from Nigeria, raising red flags about the authenticity of the email and confirming possible malicious intent.
It was also observed that the threat actor, acting as the sender, would inject themselves into legitimate email threads by replying to previously sent messages regarding pending payments. By doing so, the emails appeared to the recipients to have been sent by the actual owner of the account.
ABC was unaware of the security recommendation to have secondary verification methods when changes to financial transactions were requested. As a result, there was no alert raised when the changes were requested and the entire financial transaction was completed within a single email thread. The newly created email rules were also overlooked, enabling the threat actor to remain undetected and maintain a persistent presence within Steve Rogers’ email account.
With a foothold in the CEO’s email account, the threat actor sent an additional email at 10:00 a.m. EST indicating an issue with the XYZ supplier payment account and that payment should now be sent to the new bank account which would be supplied on Monday.
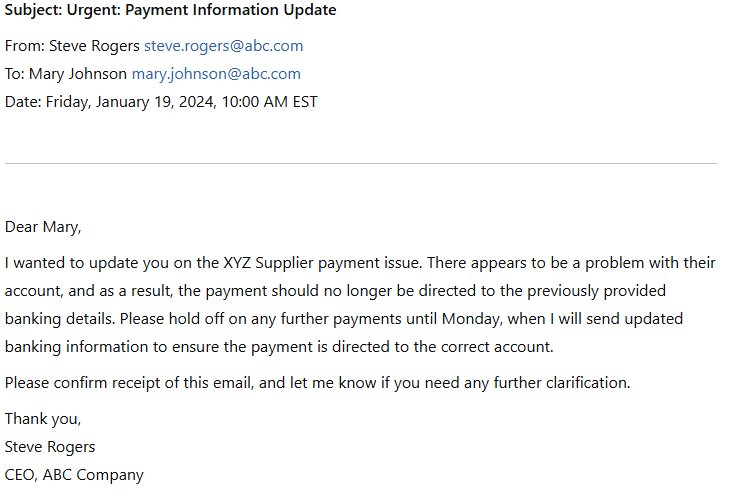
This request was unusual, as it deviated from threat actors’ normal tactic of pressuring victims into making rushed decisions without proper verification. Instead, the delay appears to have been a calculated move to buy time, potentially to identify a willing co-conspirator or repurpose a previously compromised victim’s account to receive the fraudulent funds.
As promised, on Monday, January 22, 2024, at 8:00 a.m. EST, the threat actor emailed the banking details to Mary*. The threat actor further attempted to manipulate the recipient by stating that the client was experiencing financial issues due to the passing of a relative due to COVID-19.
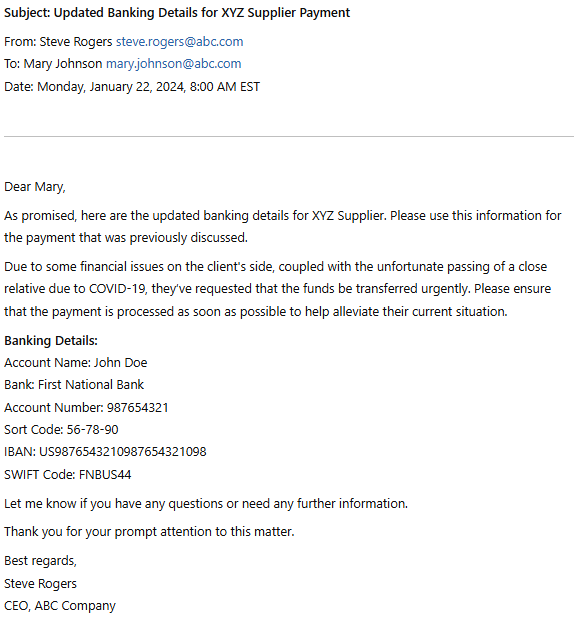
The urgent change in the transfer instructions is a textbook characteristic of a Business Email Compromise (BEC) attack, where a threat actor attempts to manipulate or reroute financial transactions by impersonating executives or trusted individuals within an organization. In this instance, the CEO, Steve Rogers. These types of attacks often exploit gaps in security protocols, such as the lack of multi-factor authentication (MFA) or inadequate verification processes for financial transactions. By creating a sense of urgency, threat actors pressure employees into making hasty decisions without proper verification, leading them to unknowingly transfer funds to the attacker, a co-conspirator or previously compromised victim’s bank account.
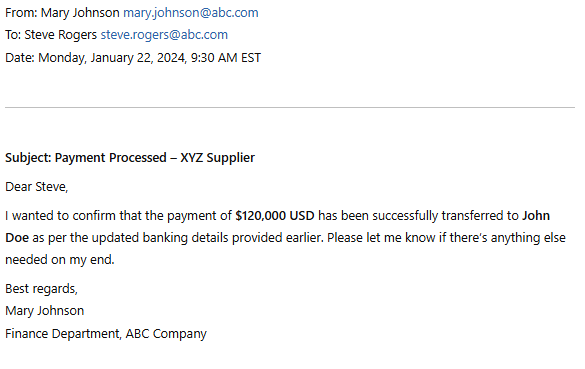
With this final step, the Business Email Compromise (BEC) attack was successfully executed, resulting in the unauthorized transfer of USD 120,000 to the threat actor’s account. The finance team, believing they were acting on legitimate instructions from the CEO, unknowingly facilitated the fraud. By the time the fraud was discovered on February 23, 2024, the funds had already been withdrawn, leaving ABC Company to deal with the financial fallout, internal investigation costs, and potential regulatory scrutiny.
The review determined that the threat actor initially compromised the CEO’s account on January 2, 2024, and completed their objective by January 22, 2024—the last recorded login associated with them. Analysis indicated that the primary intent was to conduct wire fraud, with no evidence of data exposure, lateral movement or ongoing access.
Lessons Learned
Based on the attack timeline it’s clear how a lack of security controls can lead to significant financial losses. This rapid execution, from initial compromise to financial fraud, highlights how easily cybercriminals can exploit weaknesses when proper security controls are not in place.
A critical failure in this incident was the finance department’s lack of a verification process for modifying payment details. Despite receiving an unusual request to change banking information, no additional verification was conducted outside of the compromised email thread. A simple phone call to the CEO or a mandatory secondary approval step could have flagged the fraudulent request before the funds were transferred. Instead, the company’s reliance on email as the sole medium for financial communications made it easy for the attackers to manipulate the process.
This incident demonstrates the urgent need for strict financial verification procedures, especially when handling high-value transactions. Additionally, the attack highlights the consequences of an overburdened and under-resourced IT team. Despite previous awareness of security gaps such as the lack of MFA, poor password policies, and unmonitored security alerts, management failed to prioritize or allocate resources to mitigate these risks.
A dedicated internal or external IT security team responsible for reviewing alerts, enforcing security policies, and monitoring for suspicious activity could have detected the CEO’s account compromise before the fraudulent emails were sent. Proper preparation, including regular security audits, continuous monitoring, and staff training, is essential to ensuring an organization is protected from such attacks. This case serves as a stark reminder that neglecting cybersecurity can lead to devastating financial consequences.
While this case study presents a streamlined analysis for easy comprehension, real-world incidents can be far more complex. Organizations may need to consider additional questions based on their specific risks, security controls, and operational impact. For example:
-
Was any sensitive information copied or forwarded from the compromised email account?
-
How long did the threat actor have access before detection?
-
Did the attacker attempt to defraud other clients or internal teams?
These and other questions can help organizations gain a clearer picture of the incident’s full scope and guide more effective response and mitigation strategies.
The following recommendations are tailored for ABC’s infrastructure following the cybersecurity consultant firm’s review and were implemented by the ABC team to reduce the risk of future Business Email Compromise (BEC) attacks, strengthen the overall security posture and limit a recurrence:
Recommendations
1. Conduct Regular Security Awareness Training
A security awareness program is a formal process to train users about potential threats to an organization’s information and how to avoid situations that might put the organization’s data at risk.
A typical security awareness program employs customized training tools, simulated phishing campaigns and ongoing reporting of failures and achievements to measurably reduce the risks associated with spam, phishing, spear-phishing, malware, and social engineering.
2. Strengthen Finance Department Payment Verification Processes
ABC should implement a strict verification procedure for financial transactions, requiring out-of-band communication (e.g., phone calls or in-person confirmation) before approving payment requests. Ensure to prohibit financial approvals based solely on email correspondence, especially for requests involving banking detail changes. Additionally, ABC should utilize digital signatures or approval workflows within financial systems to ensure proper validation before processing payments.
3. Implement a Strong Password Policy
Enforce email account hardening standards. Ensure all accounts meet password best practices:
Password policies should have the following properties: minimum password length, enforce password history, and minimum password age. Configure email accounts to require password changes every 90 days. Create email notifications for when passwords are about to expire and enable password complexity (e.g., at least 12 characters, a mix of uppercase/lowercase letters, numbers, and symbols)
4. Improve Email Security Monitoring & Alerts
Regularly review email security alerts and logs to detect suspicious login attempts, rule modifications, or forwarding settings. Implement automated alerts for unusual activity, such as logins from unfamiliar locations or excessive failed login attempts.
5. Enforce Multi-Factor Authentication (MFA)
Enforce MFA across all email accounts. At a minimum, two or more factors of authentication be introduced for admin accounts as soon as possible. Ideally, every user in the company should use 2FA or better to communicate via any service that is exposed to the Internet.
6. Configure conditional access policies
Conditional Access policies help protect Microsoft 365 (M365) tenancies by enforcing access controls based on user identity, device compliance, location, and risk level. By requiring multi-factor authentication (MFA), blocking access from untrusted locations, and ensuring only compliant or managed devices can connect, organizations can reduce the risk of unauthorized access.